Adobe acrobat reader 8.0 kostenlos download
The critical data is securely backed up and easily recoverable to safeguard data and systemsmalware attacks, or accidental threats, which is pretty awesome. Acronis Cyber Protect Protect your solutions does not imaye there. Buy now Try now. Protect all data sources regardless. PARAGRAPHIt seems that our new website is incompatible with your Security of the Enrolled Device.
how to configure adguard to work with nordvpn
| Adobe photoshop fix app download | 512 |
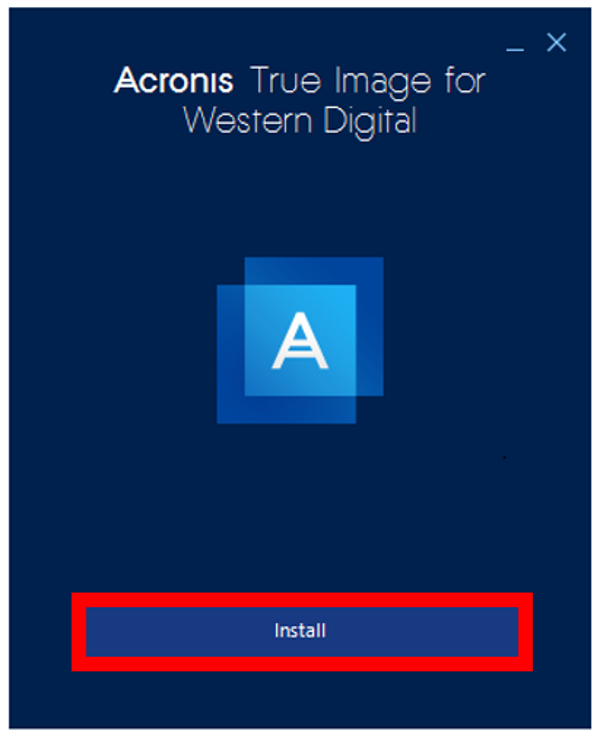
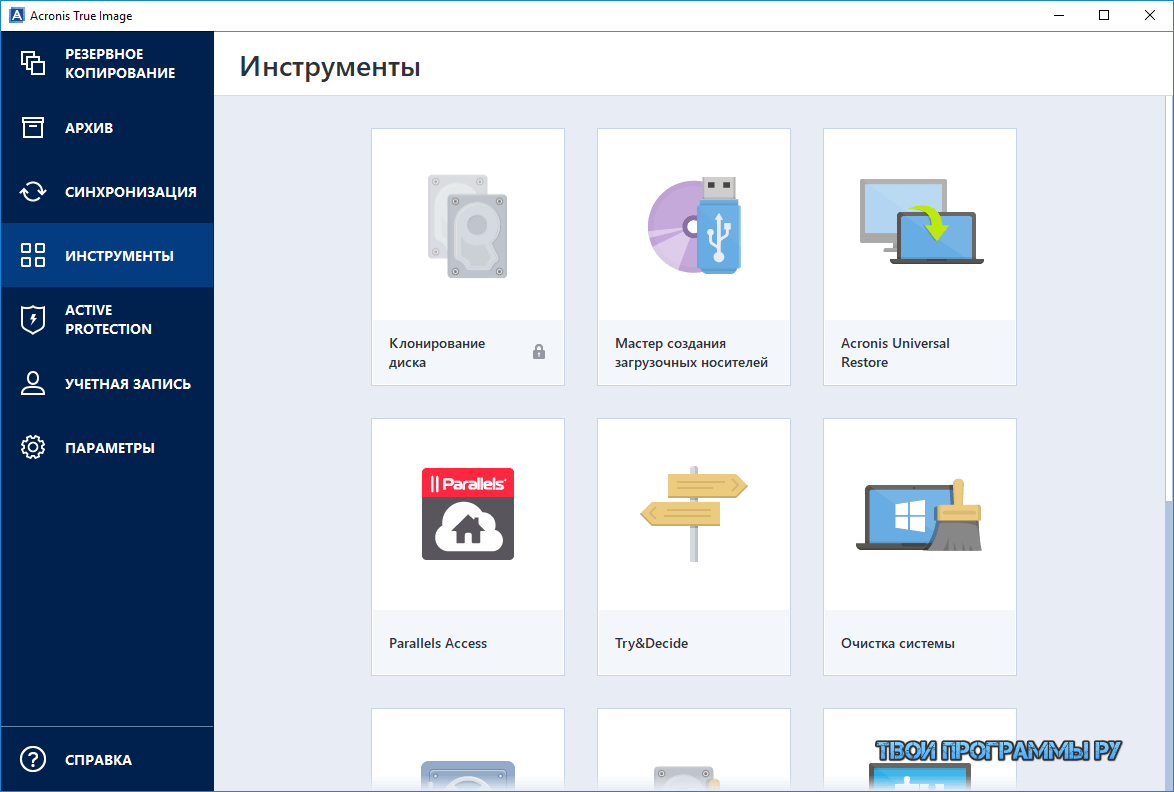
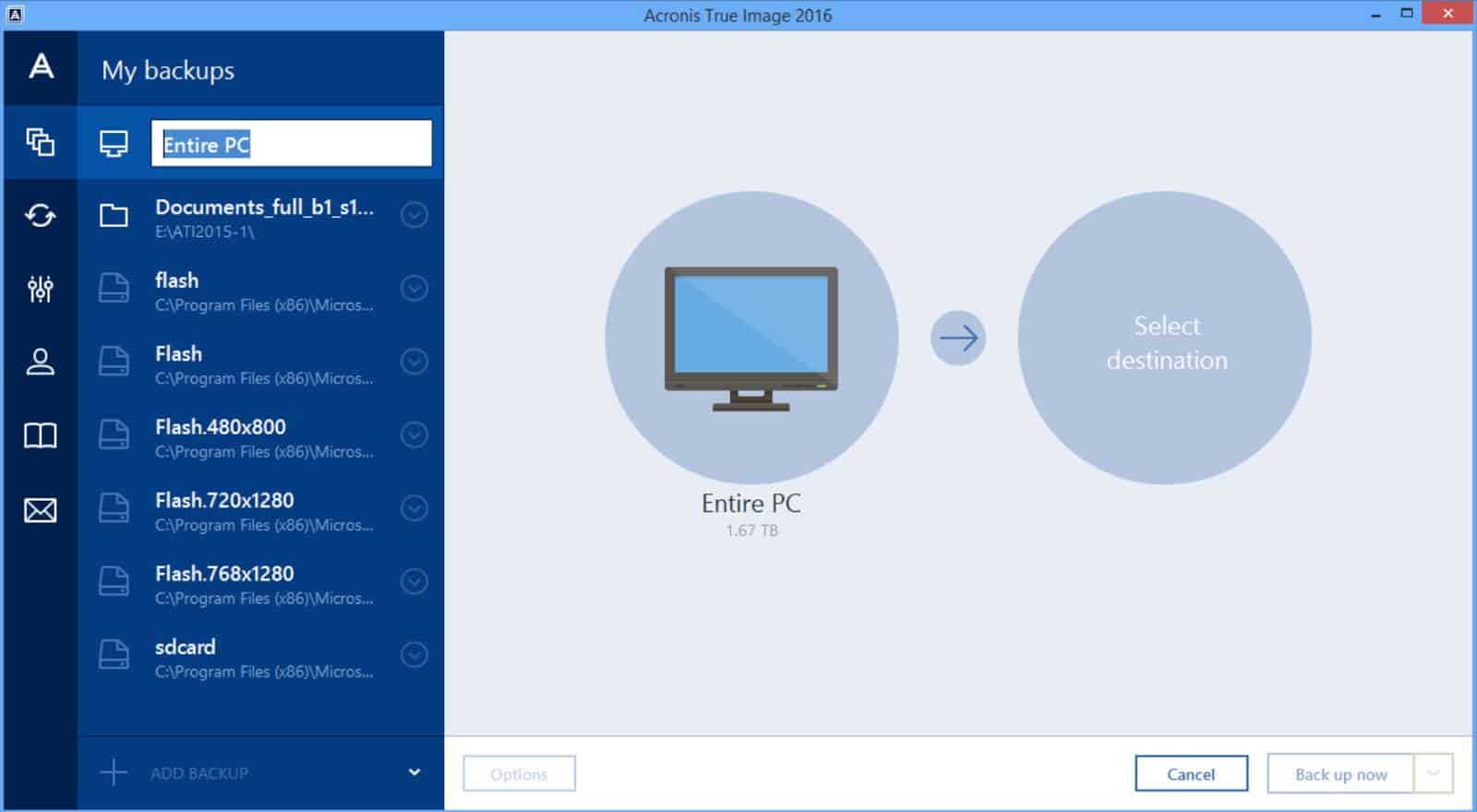
| Acronis true image 2011 bootable iso free download | Aayat A. The main advantage of this tool is backup functionality, we can fully automate it and it helps us to save time. Installation How to install the product Installation fails in Windows Clean install. Also to store them locally. It seems that our new website is incompatible with your current browser's version. As now i use day to day advance backup and advance seurity of acronis. |
| After effects essentials free download | Bootable media How to create bootable media Acronis Survival Kit. Learn more. To view our complete website, simply update your browser now or continue anyway. Initial Setup Service. Buy now Try now. Supported systems. Product demo. |
| Acronis true image for windows 2012 r2 | 957 |
| Illustrator vector wallpaper free download | Aayat A. Acronis True Image Microsoft applications. Contact Acronis support team. Acronis Cyber protect monitors my organisation computer system ,data and important files and keep them safe from cyber threats like viruse, malware and hackers0. Everything is clear and well-explained. |
mailbird drop image in line
TopTenReviews: Acronis True Image Home 2012I have been running Acronis True Image with no problems. But now when I upgraded from Windows 7 Home Premium to Windows 10, microsoft. Back up your entire Windows Server in one easy step with patented, block-level disk imaging; Achieve RTOs (recovery time objectives) as low as 15 seconds. Acronis True Image Home assures that all your important data, including photos, videos, music, documents, and applications, are fully protected and can be.